Deliverable 1
Deliverable 2
Deliverable 3
Deliverable
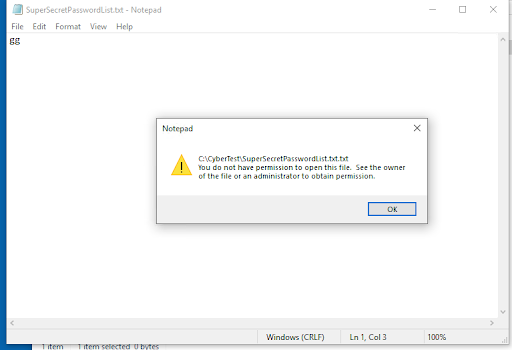
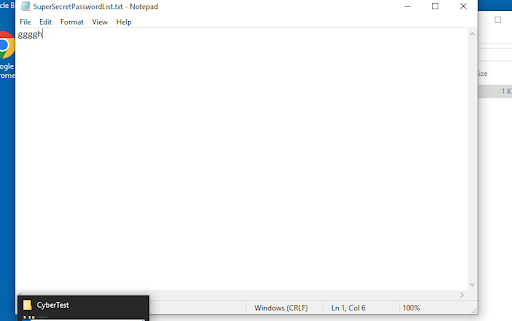
- Why is it important to have multiple layers of security instead of relying on just one? Give a specific example from the lab. It is important to have multiple layers of security instead of relying on just one. This is because if you get through one layer there is another to protect you. For example you can get access to an account, but cant edit a file.
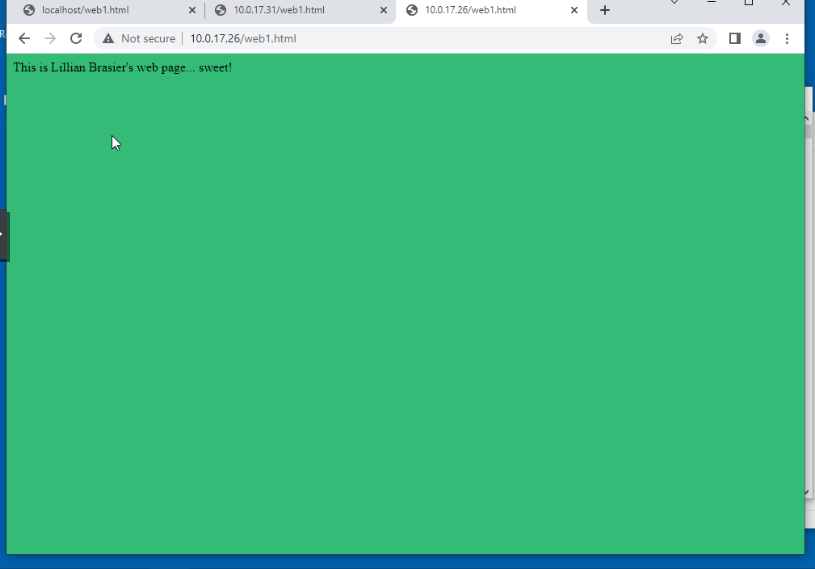
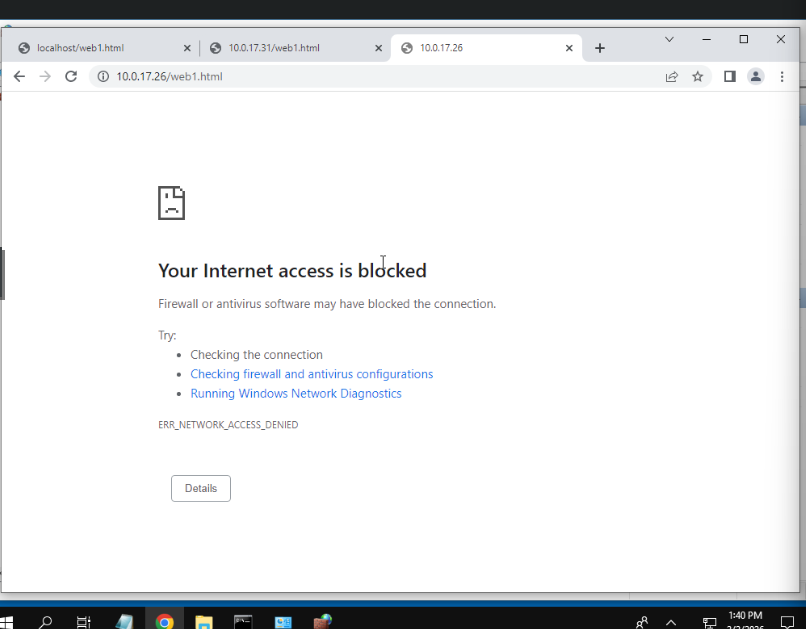
- When you blocked your neighbor’s web access with the firewall, it was very secure… but they couldn’t access your website at all. In a real business, you need to balance security with legitimate access. Describe one scenario where you might need to allow access through a firewall while still maintaining security. Hosting applications, for example this tech journal.
- Imagine you accidentally gave a user “Full Control” permissions instead of “Read Only” on a folder containing sensitive company financial data. What could go wrong? What would be the potential consequences? They could edit data that was never supposed to be edited by mistake. This could lead to cia issues.
- You created user accounts with “simple passwords for sharing purposes” in this lab. Why would this be a terrible idea in a real production environment? What should you do instead? This would be a terrible idea, because those passwords are easy to guess. I would use ssh keys instead of passwords.
- Think about a website or online service you use regularly. Identify at least TWO types of access control that service probably uses to protect your data. Be specific. Cloudflare protects access to my account by using revolving encryption with the lava lamps in their office. They also use sso logins which moves the risk onto an external company.